Leapfrog Services.
IT partnership that delivers business value.
New year, new mindset. Budget to cover the 5 key IT changes for 2023.
Download Making Sense of What’s Different for IT Budgeting in 2023.
Security and cloud.
Managed IT services from Leapfrog simplify both.

For insights to help you better understand and manage your IT, take a look at our
White Papers.
The methodologies that get you there.
Where are you now?
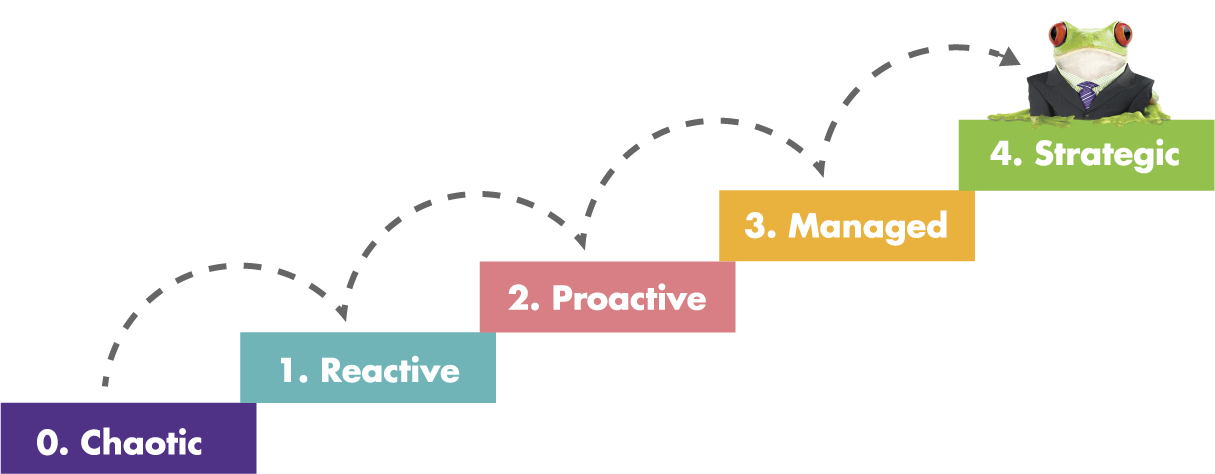
Effective IT strategy, design, and management can solve business problems and create opportunities. Whether the IT issues getting in your way are easy to identify or not, the Leapfrog Methodology pinpoints trouble areas and develops an IT roadmap to improvement that aligns with your goals.
To address security problems, our CyberRisk Program identifies, scores, and remediates cyber risk related to all four attack vectors to build a ring of security around your entire organization. Both are strategic plans based on your business priorities, including timelines, budgets, and defined roles and responsibilities.
Where do you want to go?
The Leapfrog Methodology and CyberRisk Program increase your IT and security maturity levels. By executing your IT and security roadmaps using Leapfrog’s proven frameworks, we systematically transform your IT environment into a strategic business asset and improve your ability to combat cyber risk from any attack surface.
Your IT environment becomes modernized, high-performing, holistic, and scalable, and your organization becomes more secure, resilient, and regulatory compliant. You can be more productive and worry less, and your internal teams are free to focus on activities that generate revenue, which is why you’re in business to begin with.
“From their initial role in helping us stabilize our IT infrastructure, Leapfrog’s expert managed IT services have been a great value asset to our business. Because of Leapfrog’s continued management of our IT environment, we are able to service the needs of our clients with the peace of mind that comes from knowing our data is safe and our technology works. In addition to providing great service, Leapfrog takes the time to understand our operations and proactively recommend and implement improvements in areas that add real business value.”
CIO, Large Insurance Company
Better IT means better business.
Streamlined remote working
- Unified communications
- Secure remote access
- Single sign-on
- VPNs (virtual private networks)
- VDI (virtual desktop interface, or virtual desktops)
- Redundant systems
- Leadership and manager visibility
- Monitoring and network management
Cloud clarity
- Hybrid design based on your business needs and goals
- Tools and platforms that work together behind the scenes
- Infrastructure management for a stable, secure environment
- Cloud migration planning and execution
- Intracloud connectivity and security implementation
- New platform deployment, testing, and validation
- ITIL change and service management processes
- Remote monitoring and management
IT security, bottom to top
Security that’s built-in with nonstop security monitoring protects and defends your company. Leapfrog’s CyberRisk Program covers information risk beyond technology through a ring of security that protects your entire organization against cyber loss.
- Security policies and procedures strategies — Leapfrog is a Managed Security Service Provider (MSSP)
- SSAE 18 SOC 2 compliant for organizations in regulated industries
- End-to-end data encryption
- Multi-factor authentication (MFA)
- Enhanced email security
- Ransomware-resistant backups
- DR (disaster recovery) planning and execution
- Access log reviewed by our security experts
- Monitoring and management
Happy IT users
- Deep understanding that employee and customer satisfaction and retention grow businesses
- IT environments designed to be free from glitches, delays, and complexity
- Redundancy for always-on internet
- Nonstop monitoring for anomalies and potential problems anywhere in the environment
- Apply improvements developed for one client to all clients as appropriate
- Near-instant recovery from disasters (large or small) via cloud-based DR platforms
Coordinated IT expertise
- Designs, builds, deploys, and operates hybrid IT environments
- Customizes solutions to meet your unique requirements
- Dedicated teams that specialize in all areas of IT
- Deep experience with the latest technologies
- Highest service levels for performance and security
- Participates in transformation, continuity, and budget-planning sessions
- Manages all of your IT or work alongside your internal IT team
Optimized IT processes
Well-planned and executed IT and cyber risk strategies empower your ability to do business and stay in business. Standards, consistency, automation, documentation, and accountability drive better business results.
- Proven best-practices approach with written documentation
- Consistent, verifiable results
- Strategic alignment of your IT strategy and business strategy
- IT-ecosystem perspective for utmost efficiency
- Wide range of platforms and tools, from the most common to industry-specific
- Integrated, streamlined, and secure designs
- Standardized yet flexible
- Transparent and scalable with in-depth reporting

Delivering optimized managed IT services is our passion.
So is service with a smile.
Is your IT budget on track for 2020?
How to plan, prioritize, price – and avoid common mistakes.
FrogTalk blog: Technology insights without geek speak.
We invite you to take a look at our most recent post:
Big News: We’re Going Fully AI!
We have some exciting news to share with you on this Monday. Starting today, our entire service and support will now be operated entirely by AI. That’s right, no more account managers, no more human technicians, no more phone calls or emails. Just one pure, efficient, and intelligent AI dog: Jarvis. Why did we make




