CyberRisk Beyond IT.
Leapfrog's CyberRisk Beyond IT program covers all attack surfaces.

Cyber risk management
Your information, stakeholders, and reputation are too important to risk. In today’s digitally transformed world, cyber risk is business risk.
Proven processes
Close cybersecurity gaps across non-technical attack surfaces with a comprehensive program that follows established frameworks.
Completely customizable
Your comprehensive program will align your strategy and budget with your risk profile and objectives to dramatically reduce your cyber risk.
Expert governance
With multiple specialists on your team, including an optional vCSO, you receive the highest level of cyber risk management and leadership.
CyberRisk Beyond IT is Leapfrog’s comprehensive cyber risk management program that secures your people, processes, and facilities in addition to your technology. It’s based on our Ring of Security approach to full protection that covers your entire organization.

“It’s not enough to just focus on technology for cybersecurity. You need to have a risk management approach that also covers your non-technical areas and culture of security throughout your organization. If your people think about security and follow the program every day, you’re far less likely to suffer disruptions and cyber loss.”
Bryant G. Tow, Leapfrog Services Chief Security Officer
Bryant was the managing principal of CyberRisk Solutions, a highly respected consultancy that provided cyber risk management and strike-force teams to mitigate cyber events. Leapfrog acquired CyberRisk Solutions in 2022.
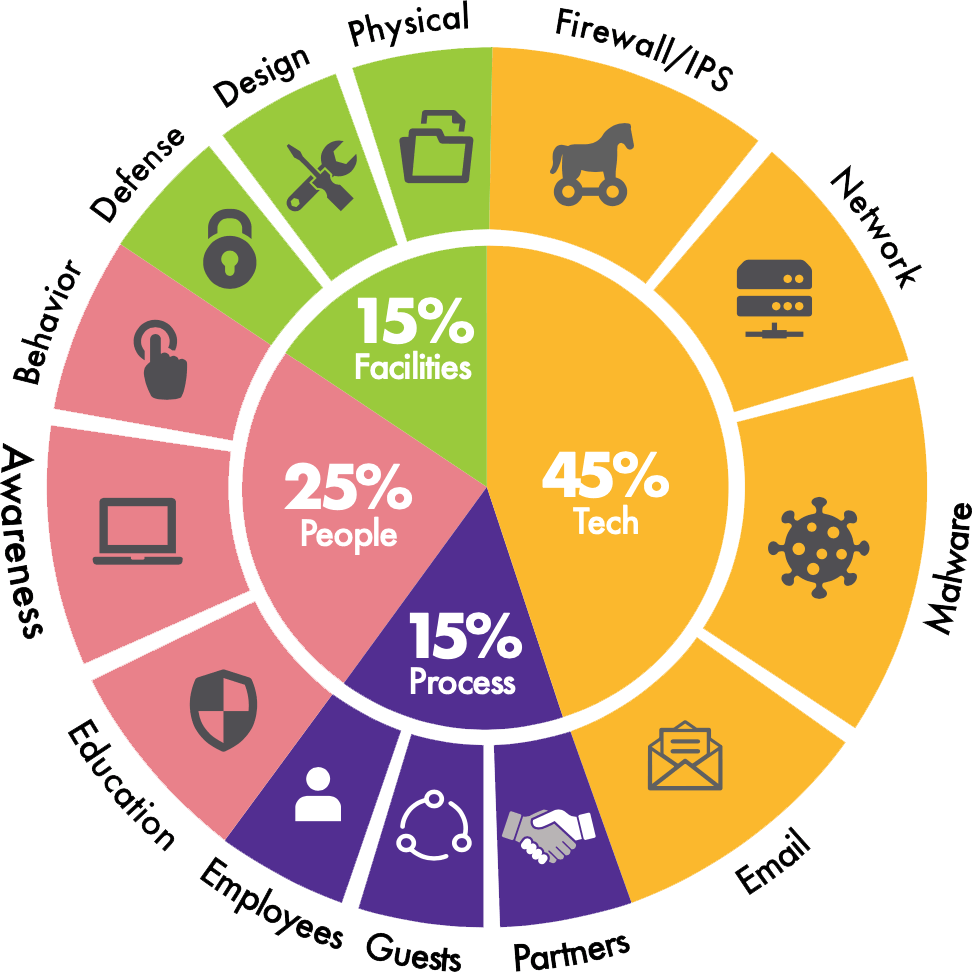
55% of your cyber risk originates with your people, processes, and facilities — not your IT.
Leapfrog’s CyberRisk Beyond IT program addresses 100% of your attack surfaces through our strategic and managed Ring of Security approach. It’s designed to protect your information and systems, fill security gaps, make improvements in priority order, and manage everything holistically. Attack surfaces in addition to technology include:
- People: Your company’s most valuable asset is also the most vulnerable. Security awareness training and new strategies guard against human error and malicious intent.
- Process: Process problems are the root cause of most breaches. Manage risk by managing processes and compliance controls across the entire organization.
- Facilities: It’s not enough to protect your digital asset perimeter — you need comprehensive visibility into your facilities, including any IoT devices.
Protect against cyber loss without slowing down business.
CyberRisk Beyond IT is designed to protect your company without getting in the way. We work in a specific order of operations when managing your program, each with a distinct phase that is proactive, overseen, and implemented in close coordination with the security leadership within your organization.
- Develop your cyber risk strategy
- Design and deploy solutions
- Continually manage program elements
- Enhance your program as risk evolves
Explore how managing cyber risk secures your entire organization:
Secure strategically
Set priorities and resource allocation so you’re taking the right actions in the right order to safeguard your business.
Govern systematically
Architect and manage policies, procedures, and processes so they operate as planned.
Lead decisively
Take advantage of vCSO experience and expertise at a fraction of the cost of a full-time CSO.
Be proactive about managing your cyber risk.
The CyberRisk Beyond IT program is for companies that understand a single weak link in any process or department can stop business in its tracks. Your customized program aligns with your business strategy and goals and amends any existing processes that create excessive financial or productivity burdens for your company.
- Scoring
- Tracking
- Budgeting
- Staffing
- Cybersecurity roadmap
- Initiative prioritization
- Program implementation
- Program governance
